SKILup Day: DevSecOps Event Recap
On August 12, 2021, the one-day virtual conference explored DevSecOps as a discipline. SKILup Day featured “how-to” lessons from speakers Alan Shimel, Kevin E. Greene, Ravi Lachhman, Taylor Smith, Bryan Finster, Colin Bell, Tracy Bannon, Peter Maddison, Scott Gerlach, Stephen Walters, Andy Suderman, Sven Ruppert, Jon Jarboe, Cindy Blake, Dr. Mark Peters, Tyler Johnson, Rob Cuddy, and Cristian Iordache.
If you missed the DevSecOps SKILup Day, we’ve got you covered with a quick round-up of the top themes that emerged from the sessions and conversations around the importance of the topic.
Why Devote a Full Day of Learning to DevSecOps?
DevSecOps is an augmentation of DevOps to allow for security practices to be integrated into the DevOps approach. The traditional centralized security team model must adopt a federated model allowing each delivery team to factor the proper security controls into their DevOps practices.
In this article published in DevOps Digest, DevOps Institute CEO Jayne Groll said, “Baking security into your software and apps from the beginning is more important than ever. Without security, your development lifecycle is open to bugs and vulnerabilities, putting your organization and customers at risk. DevSecOps is an augmentation of DevOps, allowing for security practices to be integrated into the DevOps approach. This approach shifts security to the left, ensuring that security is implemented at the beginning of the development lifecycle.”
Read more: 12 DevSecOps Trends to Watch Right Now
While DevSecOps practices are still evolving, there are many trends to keep an eye on.
SKILup Day speakers covered several trending themes, including introducing various aspects of DevSecOps, an in-depth look at integrating security into DevOps, improving pipeline security, and real-life use cases and experiences. Below we look at key quotes and discussion points from the day.
Kickstarting DevSecOps
A key theme among speakers at SKILup Day was introducing the audience to various aspects of DevSecOps, including how to get started. Many speakers had specific insights into common pitfalls and provided insight on how to avoid them.
DevOps Institute Ambassador, Stephen Walters of xMatters Inc., went back to the “basics” during his session, “DevSecOps Principles.” The session featured foundational insights from Walters on what DevSecOps is and is not and what is so different or special from DevOps. He did a deep dive into why DevSecOps is so important, the practicalities of implementing a strong solution and use cases. He also stressed that “our customers need to have trust in our ability to hold that very precious data.”
Andy Suderman of Fairwinds shared valuable insights during his session, “Do’s and Don’ts of Kubernetes Security.” Suderman stressed that DevSecOps is not a trend, and it is not going away. He then gave insight into the tools you should use and also how to ensure that Dev, Sec and Ops teams are working together for the good of the organization. Here are just a few Do’s and Don’ts that Suderman presented:
- Don’t: expect security by default using native controls
- Do: use pod security context options
- Don’t: grant access to the host node
- Do: set up a network policy
- Don’t: run containers with known vulnerabilities
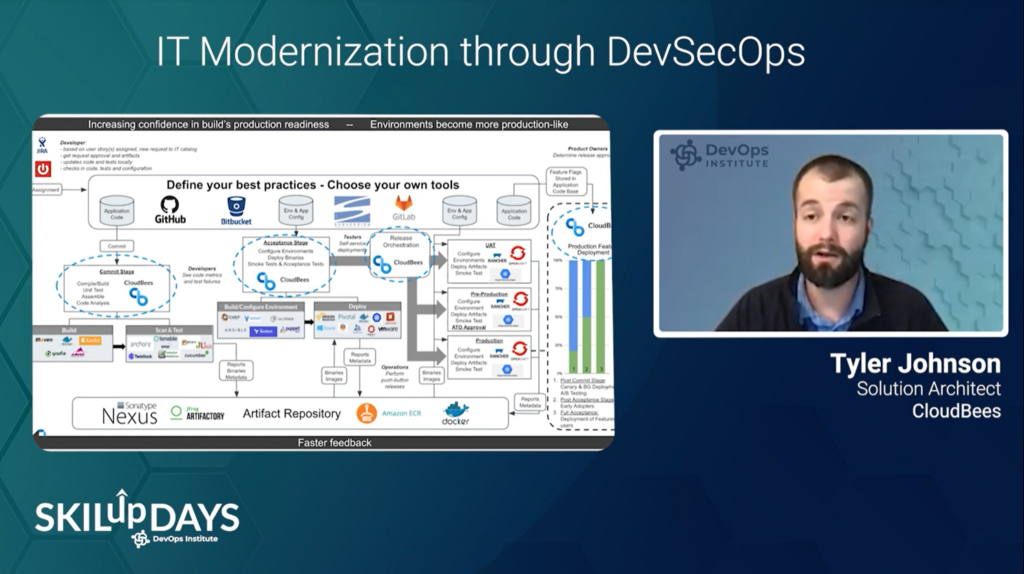
Tyler Johnson of CloudBees presented the session, “IT Modernization Through DevSecOps.” He discussed the importance of automated processes, metric collection, compliance, and continuous feedback across teams. He then explored how DevSecOps practices allow IT Modernization efforts to manage better and monitor the path to production and meet the evolving complexities of modern software delivery.
Johnson said, “It’s important to remain flexible to keep your technical debt to a minimum” when discussing choosing tools and defining your best practices.
Hey Dev! Wait a Sec…
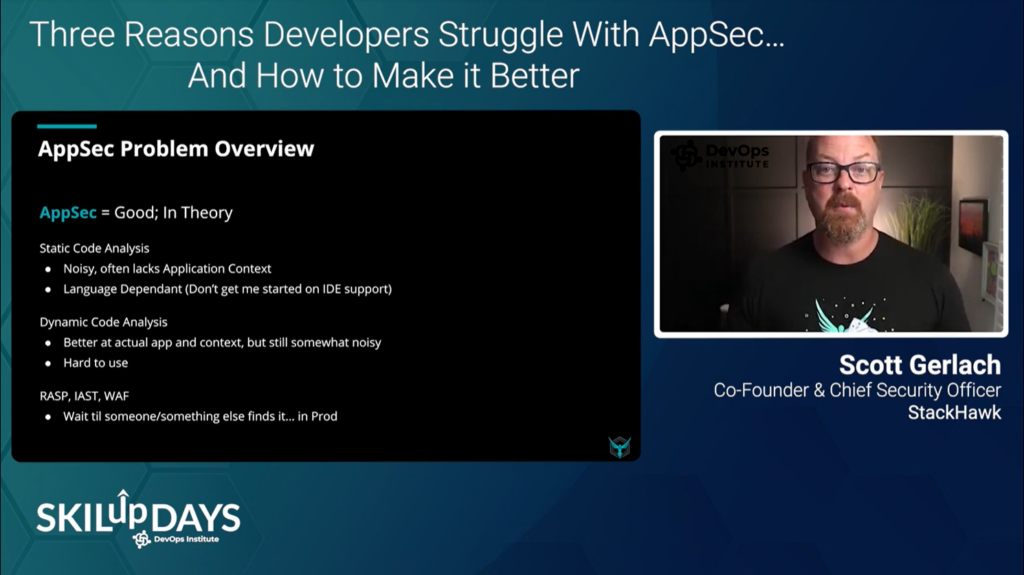
How to better enable development teams was another area of focus that emerged during SKILup Day. During his session, “Three Reasons Developers Struggle with AppSec…and How to Make it Better,” Scott Gerlach of StackHawk presented real-life learning experiences when sharing his triumphs and failures while building DevSecOps practices and tools at companies such as GoDaddy, SendGrid, and Twilio. He shared that three reasons developers struggle with AppSec are:
- The benevolent security team or lack thereof
- AppSec tools are built for security teams
- The production bias
He presented that you can “make it better” through test-driven security and instrumenting security tests into CI/CD to give engineers immediate feedback. He then emphasized to “allow technology to spark collaboration between Development and Security but enable Devs to do their work.”
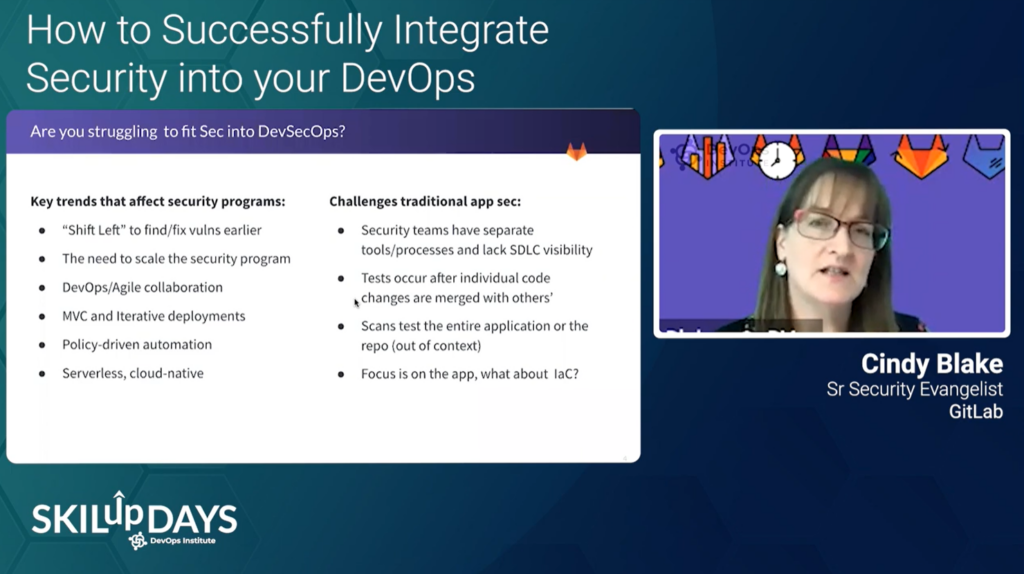
Cindy Blake of GitLab shared key insights during her session, “How to Successfully Integrate Security Into Your DevOps.” Blake explored how to mitigate risk while maintaining development velocity by focusing on the software assembly line – the CI pipeline.
She began the session with key trends that affect security programs, including shift left, the need to scale the security program and policy-driven automation. She then shared how to enable developers to address security findings in a developer-friendly way with drill-down capabilities. Blake then explained that the key to balancing application security and development velocity is testing earlier in the software lifecycle is key, along with end-to-end visibility and control.
Taylor Smith of Bridgecrew shared practical advice and tactical tips to start implementing IaC security scanning and fixing security issues right away during his session “Putting the “Sec” in DevSecOps: Automating Cloud Security as an Enabler.” He shared how (with little effort) you can adopt DevSecOps with the right training, tools, processes and strategy.
He stressed that “even with a security resource at hand, the chance of catching each bad Terraform default or hidden in a wide-open IAM policy is near impossible across endless cloud services.” He concluded the presentation with how to implement a cloud DevSecOps strategy and how to roll out your IaC governance program.
Finally, Tracy Bannon, Kevin Greene and Bryan Finster joined forces for a panel discussion: “Who’s Looking Out For the Developers??” One of the topics that they discussed was what it means to have joint ownership of security. The panelists expressed that security cannot be a stage gate. Just as quality cannot be effectively inspected at the end, security must be applied with everything we do while still enabling small, frequent changes. Tracy Bannon said, “As we push more responsibility left, we need to keep focused on security design, secure coding, upskilling/training and mentoring all those who make up a delivery organization.”
Accelerate your upskilling journey – Get certified in DevSecOps

Tightening the Valves — Pipeline Security
Many speakers had specific insights into securing the pipeline.
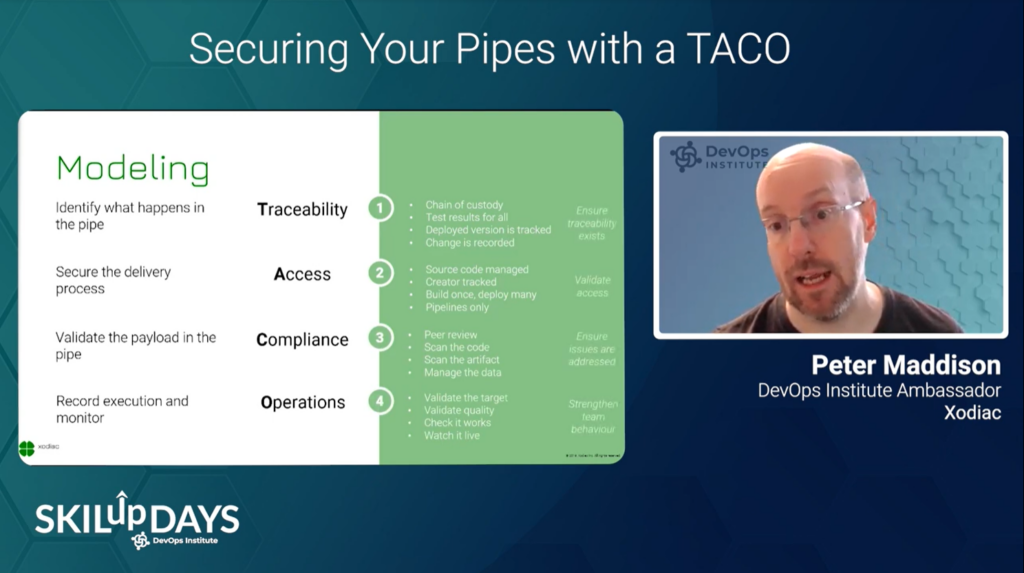
DevOps Institute Ambassador Peter Maddison of Xodiac gave first-hand advice during his session, “Securing Your Pipes with a TACO.” Maddison explained that the primary purpose of TACO is to provide a common language for the organization to understand what “good” pipelines mean for them and how to get there.
The session included insight into how taking a TACO approach can be considered a part of implementing a DevSecOps program.
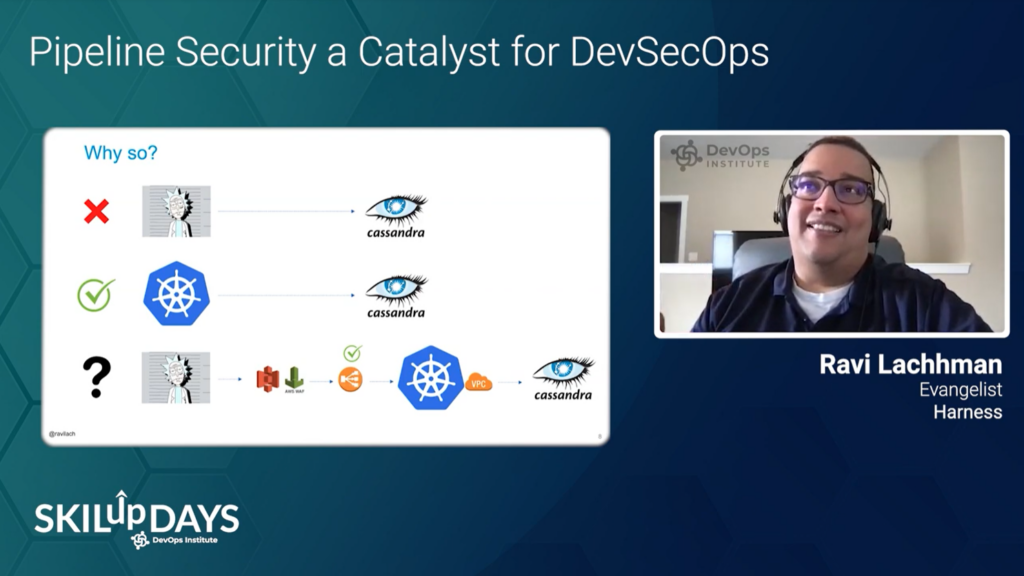
Ravi Lachhman of Harness returned for another SKILup Day. This month, he presented the session, “Pipeline Security a Catalyst for DevSecOps.” Lachhman explored how your CI/CD Pipeline can be a conduit of several security-centric steps. When discussing building security into your CI/CD pipelines, he said, “as engineers, we are under the gun to deliver with our agile sprints, making informed decisions are key.” He then shared the basics of application security terminology and several automatable methods for coverage.
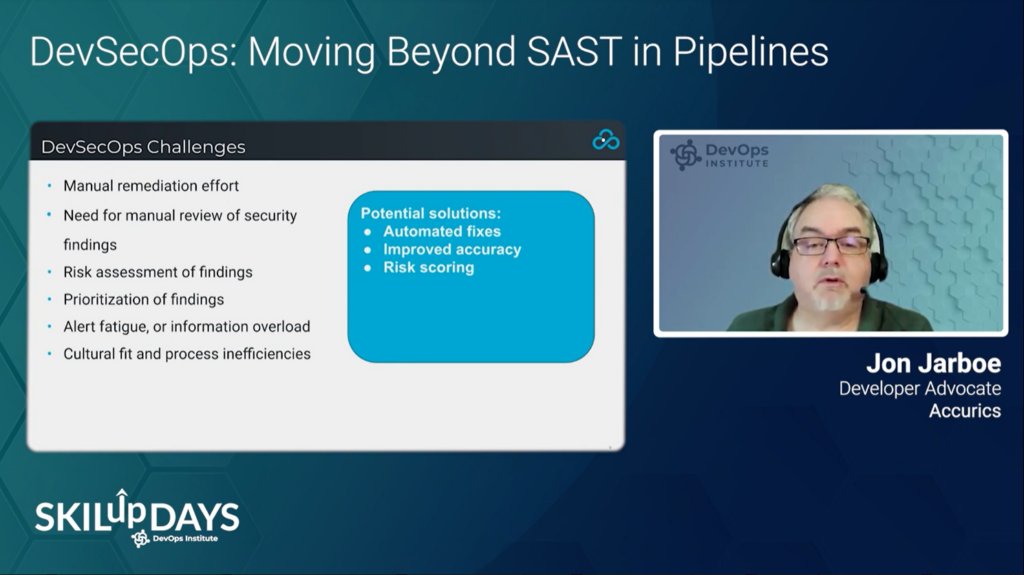
Jon Jarboe of Accurics also took on pipeline security during the DevSecOps SKILup Day. He shared valuable insights during his session, “DevSecOps: Moving Beyond SAST in Pipelines.” Jarboe emphasized that it’s tempting to believe that adding SAST scanning to your pipelines is an easy step toward DevSecOps, but the reality is that doing so can be counterproductive.
Jarboe indicated how DevSecOps teams could carefully select and configure tooling to avoid creating friction in the development process. He then shared how to leverage SAST and static analysis in automated DevSecOps processes while avoiding common pitfalls. In addition to advocating for a developer-first approach to security, he presented the following as potential solutions to DevSecOps challenges:
- Automated fixes
- Improved accuracy
- Risk scoring
12 Ways to Bake Security Into a DevOps Transformation
Experimenting with Security
Many speakers shared insights into going beyond DevSecOps. During his session, “The Major Impact of Runtime Security Controls on Risks and Efficiency,” Christian Iordache of Bitdefender explored how different runtime controls impact security effectiveness. Iordache indicated that “runtime controls remain an essential piece of the security puzzle: they prevent 0-day exploits and ensure visibility into runtime anomalies, potential attacks, and the containers and pods impacted.” He then proposed how cloud workload protection platforms can automate and streamline your security workflows.
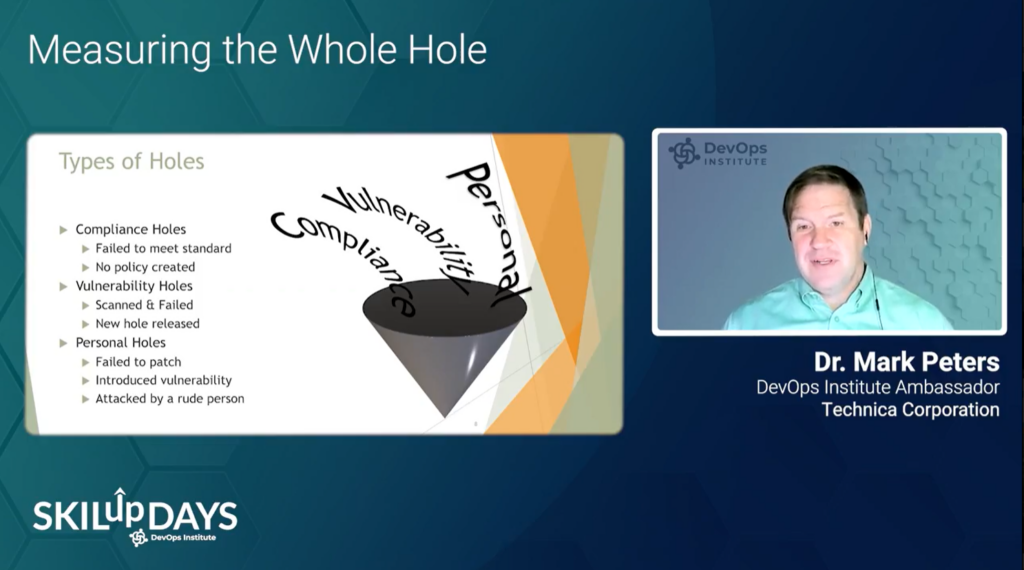
DevOps Institute Ambassador Dr. Mark Peters of Novetta presented the session, “Measuring the Whole Hole.” During his session, he discussed integrating requirements and automating non-vulnerability standards. He also explored using unified mark-up language integrated requirements and how common tools can link users, integrate contingency plans, and expedite compliance to increase value. He did a deep dive into identifying and measuring various holes, including compliance holes, vulnerability holes and personal holes.
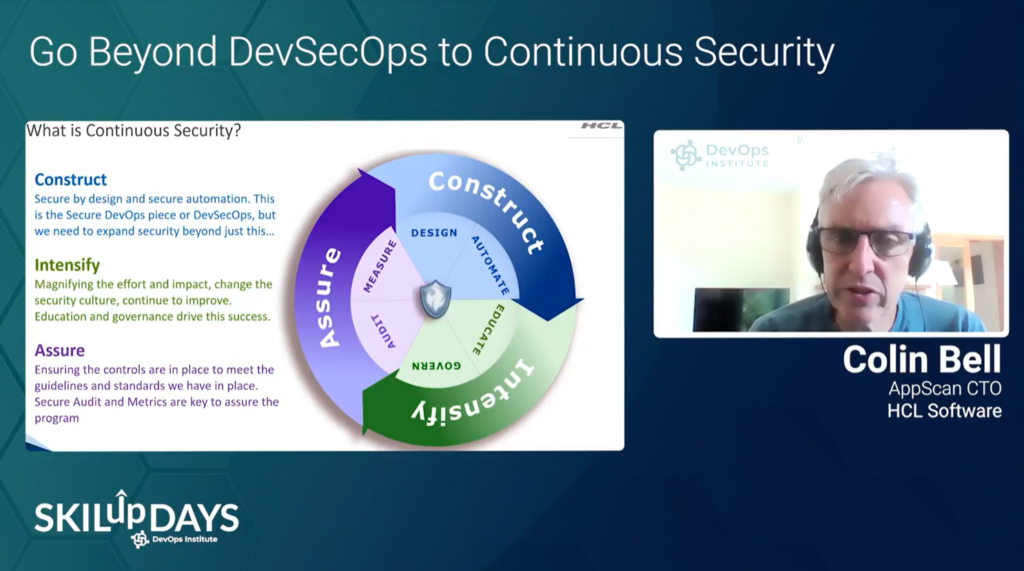
Rob Cuddy and Colin Bell of HCL Software teamed up for the session “Go Beyond DevSecOps to Continuous Security.” They emphasized that “the current thinking around DevSecOps traditionally focuses on adding security practices to pipelines. This is a great thing, but it is not enough.” They gave tangible advice on the phases of implementing Continuous Security.
Finally, Sven Ruppert of JFrog stressed that attacks like the “Solarwinds Hack” are becoming more and more sophisticated and that the attackers now focus on the entire value chain. His session, “The SolarWinds Hack and the Executive Order on Cybersecurity Happened – It is Time to Prepare,” explored how you can prepare for the challenges of cyberattacks.
What’s Next?
Get advanced-level DevSecOps technical concepts, learn about DevSecOps architecture and infrastructure strengths, and gain an understanding of the many steps associated with pipeline security principles (ensuring items are not just sooner and safer but more secure as well). Plus learn how DevSecOps may evolve in the following years.



![[EP112] Why an AIOps Certification is Something You Should Think About](https://www.devopsinstitute.com/wp-content/uploads/2022/01/DOI-Human-DevOps-Digital-Podcast-Screen-600x600px-400x250.jpg)

